Practical Binary Analysis
Practical Binary Analysis covers all major binary analysis topics in an accessible way, from binary formats, disassembly, and basic analysis to advanced techniques like binary instrumentation, taint analysis, and symbolic execution. Order a hardcopy or ebook online at No Starch Press or from your favorite bookstore, or download a free sample chapter.
Translations
Practical Binary Analysis is now available in Polish, Korean, Japanese, and Chinese (Mandarin)!
Virtual Machine and Code Samples
The book comes with a virtual machine that contains all the examples and software. You can download it from this torrent. The username and password for the VM are both “binary.” To use the VM you'll need VirtualBox. You can also download just the example code.
Important: Make sure to update the VM to ensure that any errata are fixed. You can always get the latest updates by opening a terminal on the VM and running the following command:
cd /home/binary && rm -f auto-update.sh \
&& wget -q --no-check-certificate https://practicalbinaryanalysis.com/patch/auto-update.sh \
&& chmod 755 auto-update.sh && ./auto-update.sh
Note that you should use only the above command to update. Updating the OS or any software packages, for instance with apt, is not recommended because some of the pre-installed binary analysis toolkits have very specific expectations about the system.
Update: On September 31st 2021, the Let's Encrypt root certificate expired. As the new root certificate is not present on the VM, wget now requires the --no-check-certificate option to download updates from the book website. All of the patch scripts have been updated accordingly.
Running Code Samples on Windows and Other Platforms
If you know what you're doing and you really want to run the code samples on a platform other than the VM, that should be possible in most cases. Most of the tools used in the book, including Capstone, Pin, and Triton, are made to work on Linux, Windows, and macOS. The major exception is libdft; unfortunately, porting it to Windows is probably hopeless without a major rewrite.
Triton and libdft depend on older Pin versions that don't work on Linux kernel 4.4+. Therefore, getting these tools to work on a modern Linux distro can be a challenge. If you still want to attempt this, you may want to skim my notes on getting Pin 2.13, Pin 2.14, and libdft to work on Ubuntu 16.04. Note that this involves downgrading the kernel, which is not recommended for any kind of production system.
Downloads
- Virtual machine with all code samples and software (username/password “binary”) Magnet link Torrent file
- Virtual machine (direct download w/ limited data, please use only if you can't use the torrent) VM (.ova)
- Archive with all code samples Archive (.tar.gz)
- Patch for libdft Patch file
- Sample chapter on basic binary analysis PDF
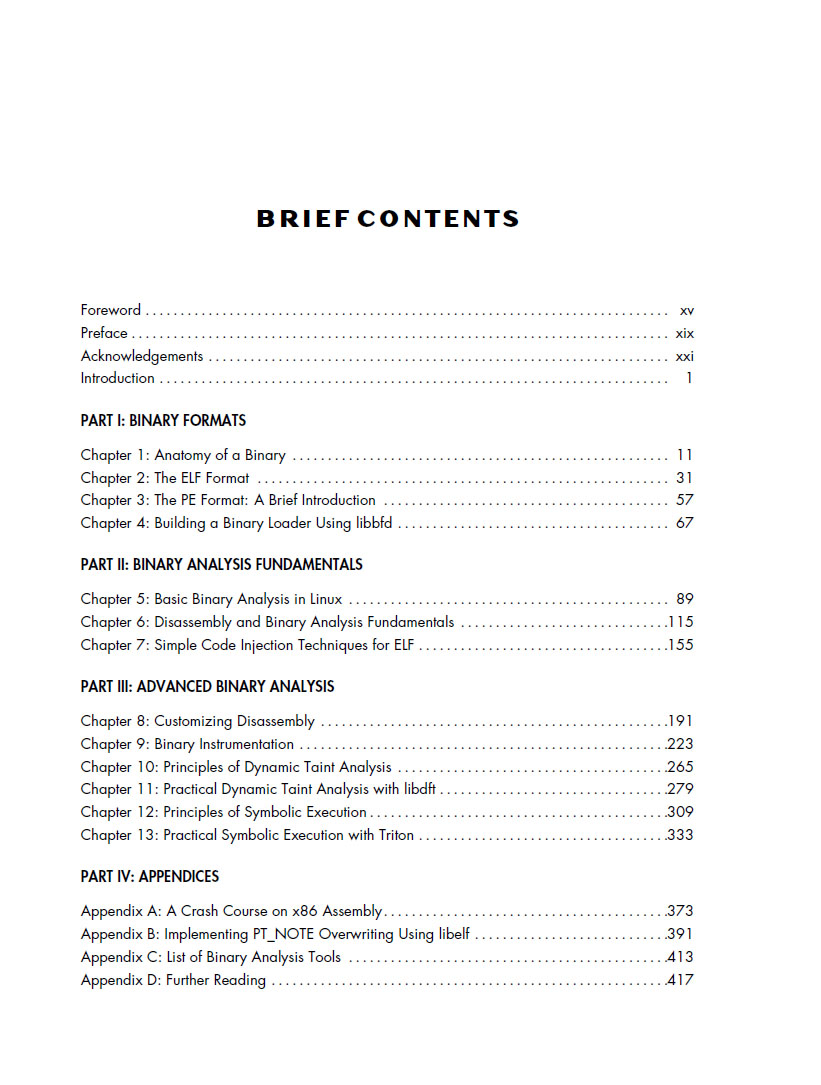
- Table of contents PDF
Errata
Please report any factual or typographic errors in the book to No Starch Press or to the author at da.andriesse‹ατ›gmail.com. The current list of errata is available here.
Community Contributions
Made something cool? Let me know and I'll add it to the list!
CTF Walkthroughs
- Chapter 5 CTF walkthrough @ Nucu Labs lvl2
- Chapter 5 CTF walkthrough @ Cool|Byte lvl1-lvl4 lvl5
- Chapter 5 CTF walkthrough @ Matteo Malvica lvl6 lvl7
- Chapter 5 CTF walkthrough @ Miles Mulet lvl8
- Chapter 5 CTF walkthrough @ Loïc Pefferkorn lvl2-lvl4 lvl5-lvl7 lvl8
Exercise Solutions
- 0xe1a00000's examples and solutions to selected exercises Github
- Fast, parallel, cross-variant ROP/JOP gadget finder (expanded solution to Ch8 exercise) Github
- lucadidomenico's solution to the Ch11 format string vulnerability exercise Github
- Fare9's solutions to the Ch12 exercises Pastebin
- lucadidomenico's solution to the Ch13 license key exercise Github
Code and Tools
- Fare9's custom versions of the PBA tools Github
- Rat Fink's custom and updated versions of PBA tools, and notes on further reading Github
Contact
In case of questions or comments, contact me at da.andriesse‹ατ›gmail.com.
PGP key
Here's my [PGP key].PGP key fingerprint
A82C A27D 4A27 CF84 7C23BC58 BAD7 CA8E F693 94DD